About DMZ (Demilitarized Zone)
DMZ is responsible to enhance the security of an organisations network by separating local area network from other untrusted network.
DMZ in Nutshell
- DMZ stands for a demilitarized zone.
- DMZ is use to improve the security of an organisation’s network.
- DMZ is a physical or sensible subnet that separates LAN (local area network) from other untrusted networks.
- Hacker could use this as an opening to cause havoc on the company’s network.
- The most common of these services include web, email, domain name system (DNS), File Transfer Protocol (FTP) and proxy servers.
- A DMZ network has limited access to within organize.
- Examples of DMZ :- Cloud services, Home networks, Industrial control systems .
Architecture and Design
These are two Architecture
- Single Firewall DMZ Network
- Dual Firewall DMZ Network
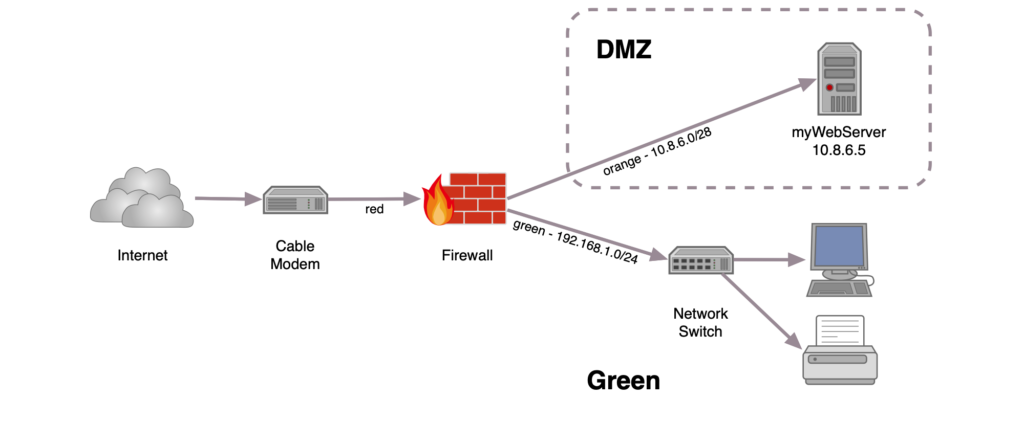
Single Firewall DMZ Network
- A DMZ with a single-firewall design requires three or more network interfaces.
- The first is the external network, which connects the public internet connection to the firewall.
- The second connects is the internal network.
- The third is connected to the DMZ.
Dual Firewall DMZ Network
- A DMZ with a Dual Firewall design requires two network interface.
- The principal firewall just permits outside traffic to the DMZ.
- The second just permits traffic that goes from the DMZ into the inside organization.
.
Advantages of DMZ
- Access control.
- Network reconnaissance prevention.
- Blocking Internet Protocol spoofing.
Services of Utilizing a DMZ
- Domain name system (DNS).
- File Transfer Protocol (FTP).
- proxy servers.
- WEB server.
- Mail Server.
A DMZ divided a network into 2 parts firewall.
- Inside the firewall
- Outside the firewall.
This DMZ setup only uses one farewall.
Conclusion
- In the real world.
- A demilitarized Zone.
- it is an area where the military is forbidden or in the computer world.
- it is where Firewall protection is forbidden.
0 Comments